SentinelOne
SentinelOne
Overview
The SentinelOne integration connects the Praetorian Guard Platform (PGP) with SentinelOne's endpoint detection and response (EDR) platform to import managed endpoints, agent status information, and threat detections. By ingesting data from SentinelOne, PGP gains visibility into your endpoint security posture and can correlate endpoint assets with the broader attack surface.
Endpoints are a critical component of any organization's attack surface. The SentinelOne integration ensures that PGP has an accurate and current inventory of all endpoints managed by SentinelOne, including their agent health status, operating system details, and network information. This enables security teams to identify gaps between known assets and protected endpoints, and to understand which systems have active threat detections.
This integration uses the SentinelOne Management Console API v2.1 in a read-only capacity. PGP queries SentinelOne for agent and threat data and does not modify any configurations, policies, or threat responses in your SentinelOne environment.
What the Integration Does
The SentinelOne integration connects to your SentinelOne Management Console via the REST API to retrieve agent inventory and threat detection data. For each agent registered in your SentinelOne environment, PGP imports the endpoint as an asset, capturing details such as hostname, IP addresses, operating system, agent version, and agent health status.
When threat import is enabled, the integration also retrieves active and resolved threat detections, allowing PGP to incorporate endpoint threat intelligence into its risk model. The integration validates connectivity by querying the accounts endpoint before proceeding with data import.
All operations are strictly read-only. PGP does not modify agent configurations, initiate scans, trigger responses, or alter any threat status in your SentinelOne console.
Prerequisites
Before setting up the SentinelOne integration, ensure you have:
A SentinelOne Management Console with API access enabled
An API Token with read permissions for agents and threats
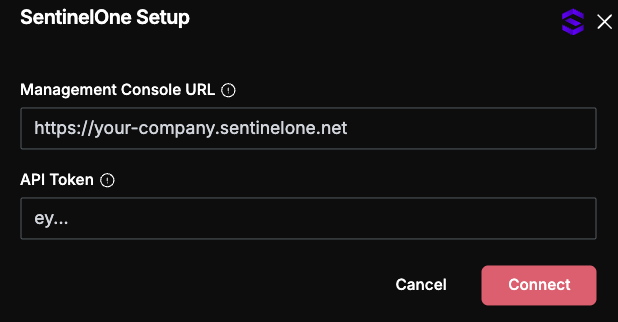
The console URL for your SentinelOne Management Console (e.g.,
https://your-company.sentinelone.net). Customers in other regions will see a regional prefix on the hostname, such asusea1-,eu1-, orapse1-(for example,https://usea1-yourcompany.sentinelone.net).
Creating an API Token
Sign in to your SentinelOne Management Console.
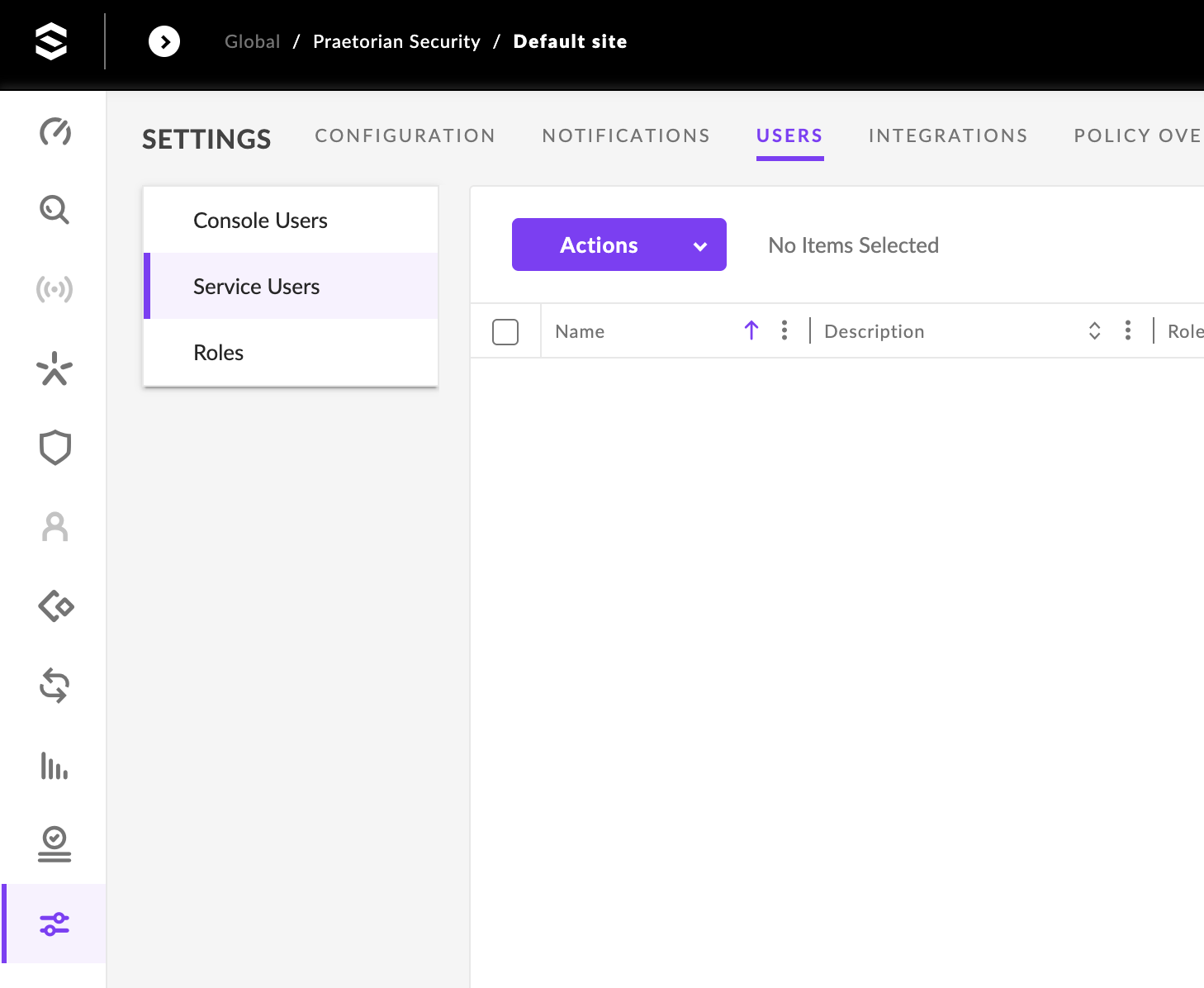
Navigate to Settings > Users > Service Users (not Console Users).
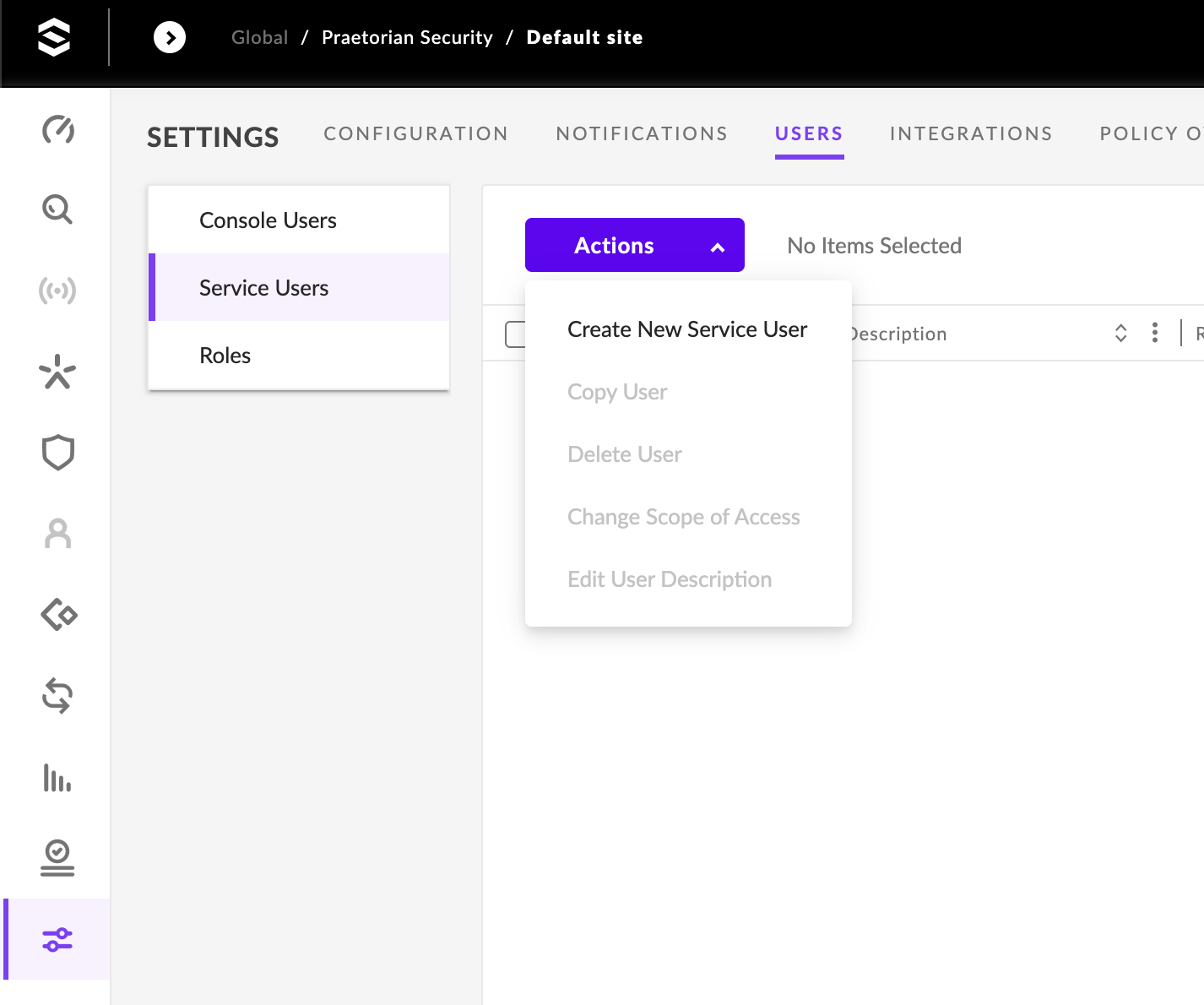
Click Actions > Create New Service User. Service Users cannot log into the Console, are designed for API integrations, and decouple PGP's access from any individual employee.
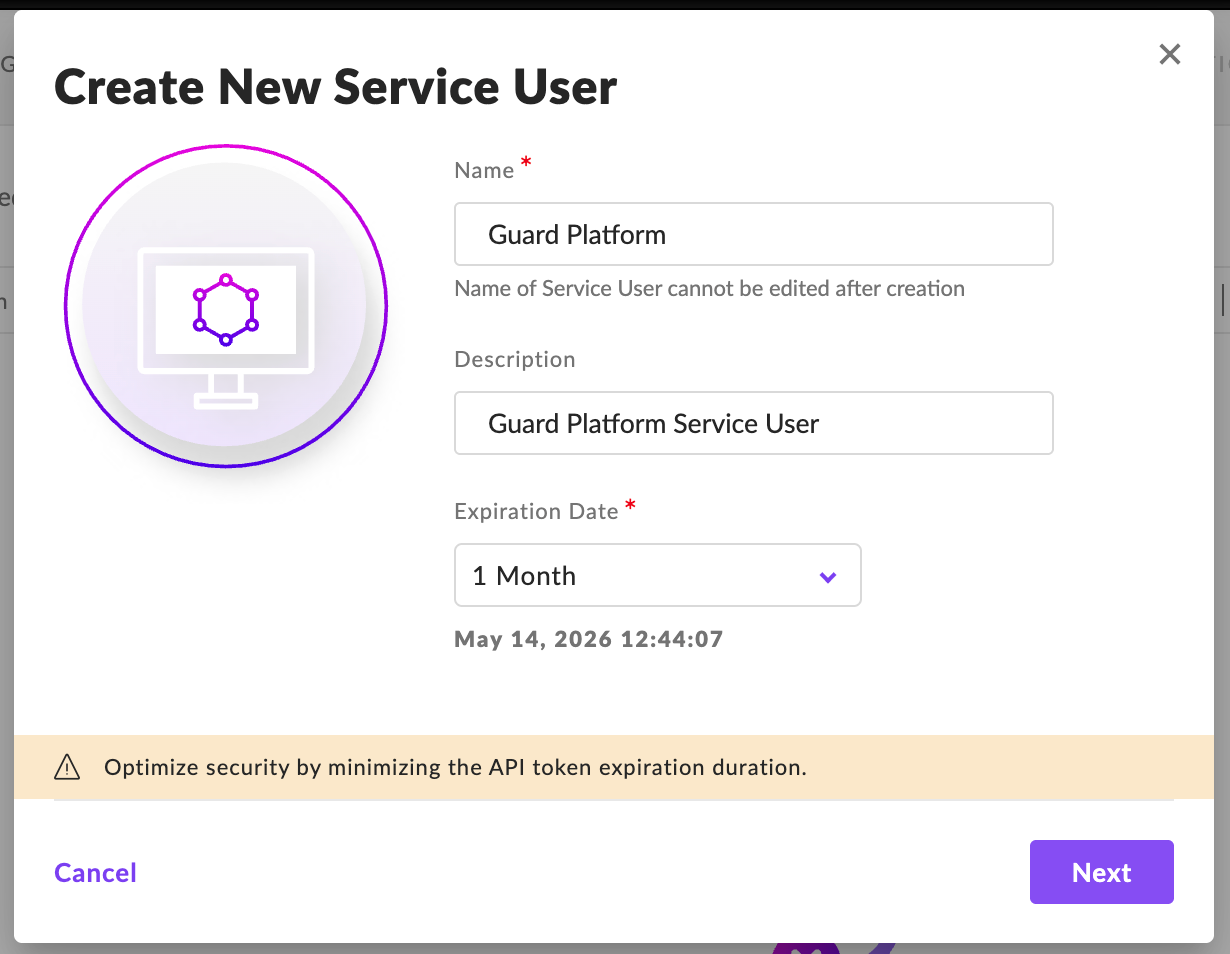
Set the Name, Description, and Expiration Date for the service user.
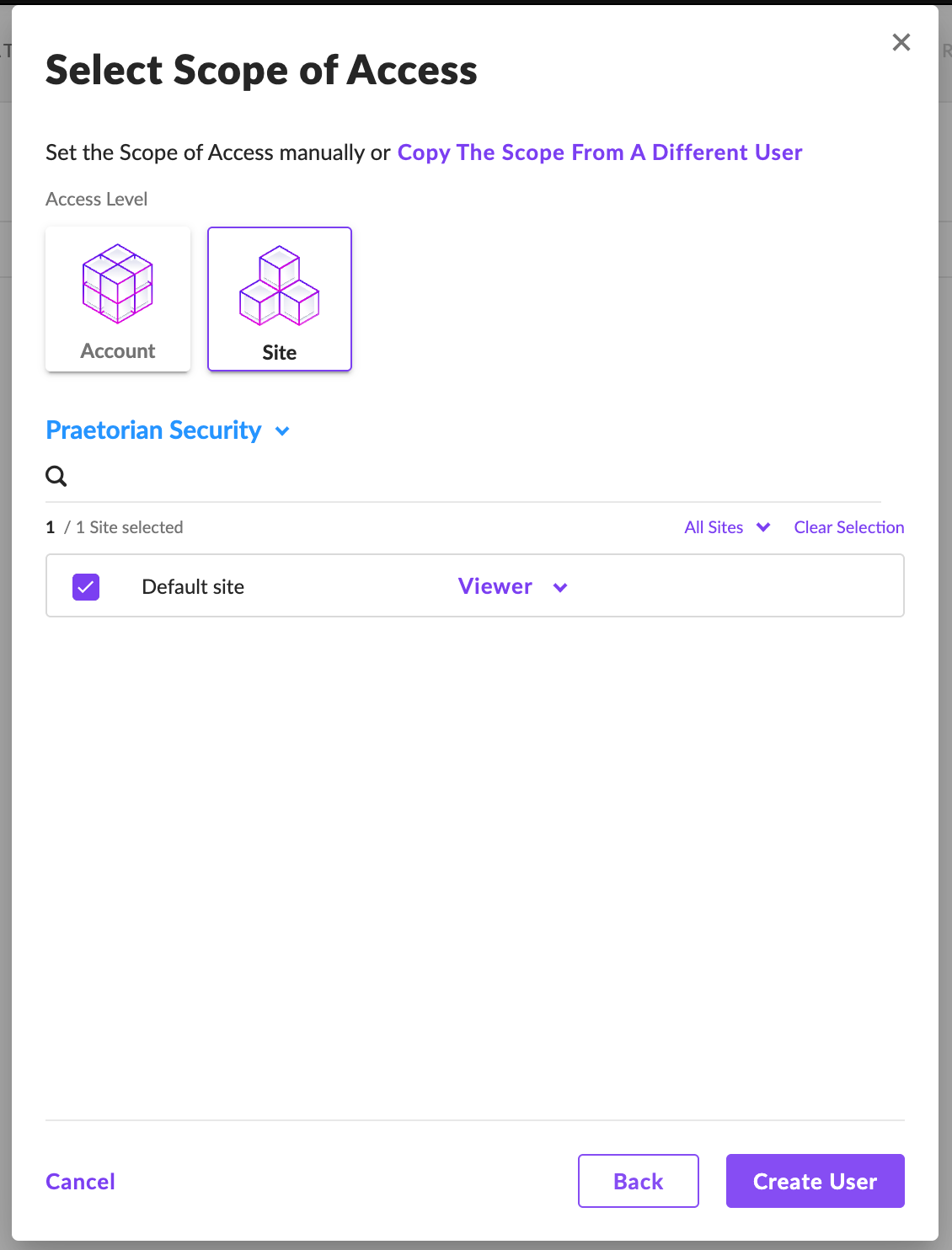
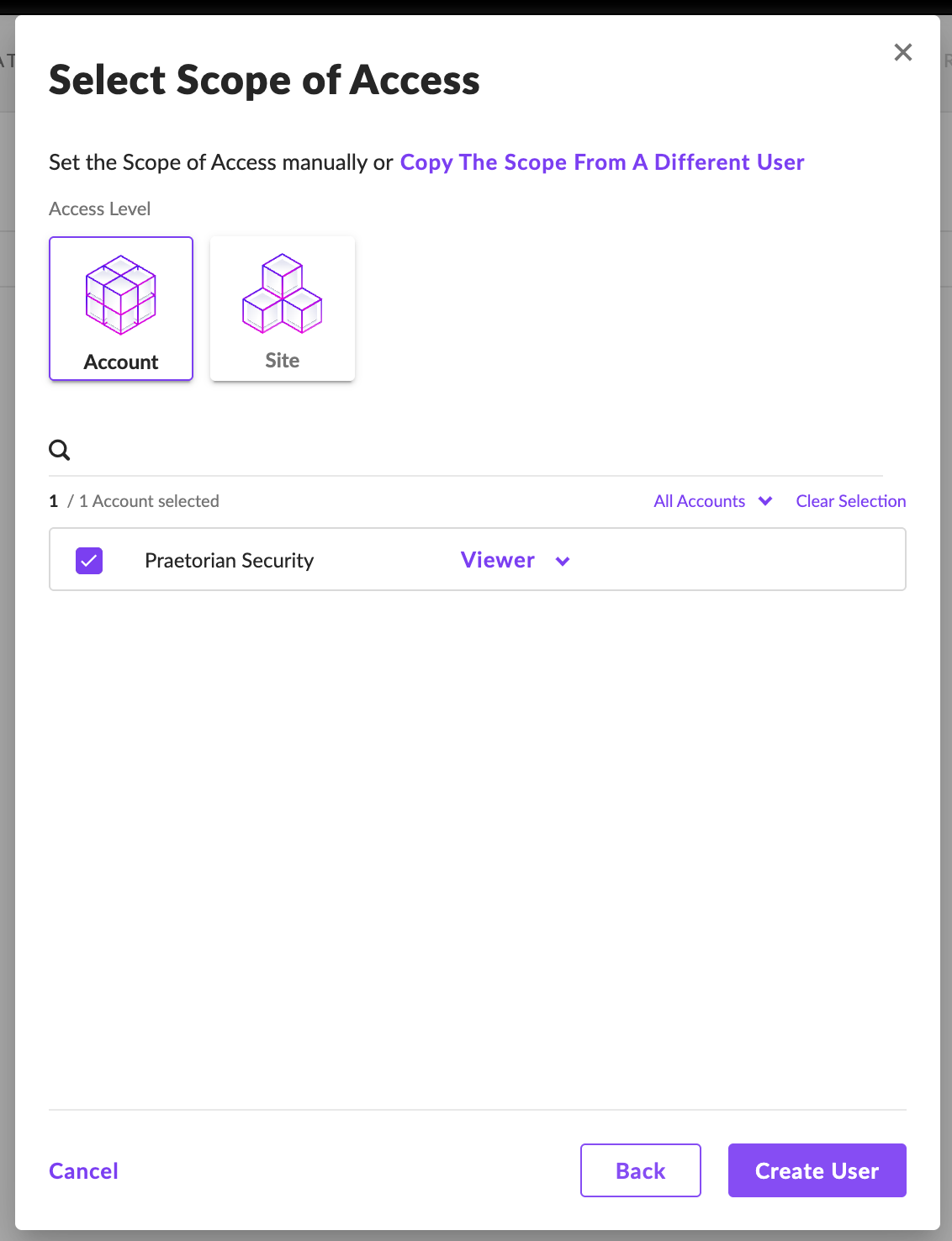
Set the Scope of Actions for the Service User for either the Account or Site level and then click Create User.
Click Actions > API Token Operations > Generate API Token.
Ensure the Service User's role grants the following permissions:
Accounts.viewEndpoints.viewThreats.viewSDL Data.viewEdr— for threat hunting (Deep Visibility queries)
The built-in Viewer role covers the
.viewpermissions for asset and threat sync. For threat hunting, duplicate the Viewer role, addSDL Data.viewEdr, and assign the new role to the Service User.Deep Visibility requires the Singularity Complete SKU. If your tenant is on Singularity Core, DV is unavailable regardless of role configuration.
Warning -- the API token is displayed exactly once. SentinelOne does not let you re-view it. Copy it immediately into a secrets manager. To rotate the token, you must delete and recreate the Service User.
Setup
In PGP, navigate to the Integrations page.
Select SentinelOne from the list of available integrations.
Enter your SentinelOne console URL and API token in the configuration form.
Save the integration. PGP will validate connectivity to the SentinelOne API by querying the accounts endpoint.
Note -- static egress IPs. PGP connects to SentinelOne from a fixed static IP pool, which can be allowlisted in your console's network policy if you restrict API access by source IP.
Field Reference
What Data Is Synced
Endpoints / Agents (Assets)
The integration imports all managed endpoints from SentinelOne as assets into PGP.
Threat Detections (Risks)
When threat import is enabled, the integration retrieves threat detections from SentinelOne.
API Endpoints Used
The integration paginates through agent and threat data using SentinelOne's cursor-based pagination. All requests are authenticated using the API token passed in the Authorization: ApiToken header.
Required API Permissions
Troubleshooting
Security and Data Handling
The SentinelOne integration operates in a strictly read-only mode. It queries the SentinelOne Management Console API to retrieve agent and threat metadata and does not modify any agent configurations, trigger scans, initiate threat responses, or alter any settings in your SentinelOne environment.
Credentials are handled securely within PGP. The SentinelOne API token is encrypted at rest and used exclusively for authenticating API requests during sync operations. The token is not exposed in logs or transmitted to any third party.
PGP imports only endpoint metadata and threat detection summaries. No endpoint file content, forensic data, quarantined samples, or response actions are accessed or stored by PGP.