Palo Alto Networks Panorama
Integrate with Panorama
Overview
The Palo Alto Networks Panorama integration brings your firewall-managed network inventory into the Praetorian Guard Platform (PGP), giving you visibility into assets that your firewall infrastructure already knows about but that may be missing from your attack surface. Panorama centrally manages address objects — the IPs, CIDR blocks, FQDNs, and IP ranges that define your protected environment — and this integration imports them directly into PGP as assets without any manual data entry.
This is especially valuable for organizations managing large-scale firewall deployments across multiple device groups. Rather than reconciling Panorama and PGP separately, the integration automatically surfaces firewall-managed assets so they can be assessed, scanned, and tracked as part of your broader security posture. If Panorama knows about an address that PGP hasn't discovered through external scanning, you'll see it — closing gaps in your attack surface coverage.
What the Integration Does
The integration is read-only: PGP queries your Panorama instance's REST API and imports address objects as assets. It does not modify any configuration, policies, or objects in Panorama.
How it works:
Authentication — PGP authenticates to your Panorama REST API using the API key you provide, passed via the
X-PAN-KEYheader over HTTPS.Address object enumeration — PGP queries the
Objects/AddressesandObjects/AddressGroupsendpoints to retrieve all address objects from your configured scope (a specific device group or the shared address space).Asset creation — Each address object is mapped to a PGP asset and tagged with the
paloaltocloud service identifier, linked back to its originating device group.Affiliation tracking — On subsequent runs, PGP checks whether previously imported assets still exist in Panorama. If an address object is removed from Panorama, PGP detects the change.
Imported Address Types
Address groups (both static and dynamic) are also discovered for metadata enrichment, providing additional context about how your firewall policies organize these assets.
Scoping
If you specify a device group during setup, only address objects within that group are imported. If you leave the device group field blank, PGP queries the shared location, pulling in address objects available across all device groups.
Prerequisites
Before setting up the integration, you need:
A Panorama instance accessible over HTTPS from PGP
An API key generated from a Panorama administrator account with read access to address objects
Network connectivity between PGP and your Panorama instance — if Panorama is behind a corporate firewall, ensure appropriate access is configured
Creating an API Key
Log in to the Panorama web interface
Navigate to Device > Administrators (or use the XML API
keygenendpoint:type=keygen&user=<USER>&password=<PASS>)Generate a new API key for a user account with at least read-only access to Objects
Copy the key — it is displayed only once
Recommended Permissions
For least-privilege access, create a custom admin role in Panorama:
Alternatively, the predefined Superuser (Read Only) role works but grants broader access than necessary.
PAN-OS version note: PAN-OS 10.2 and later provide separate permission tabs for REST API and XML API, allowing more granular control. The integration defaults to REST API version v11.1. If your Panorama instance runs an older PAN-OS version, you can specify a different API version during setup.
Setup
In PGP, navigate to Integrations and locate Palo Alto Networks Panorama under the Firewall category.
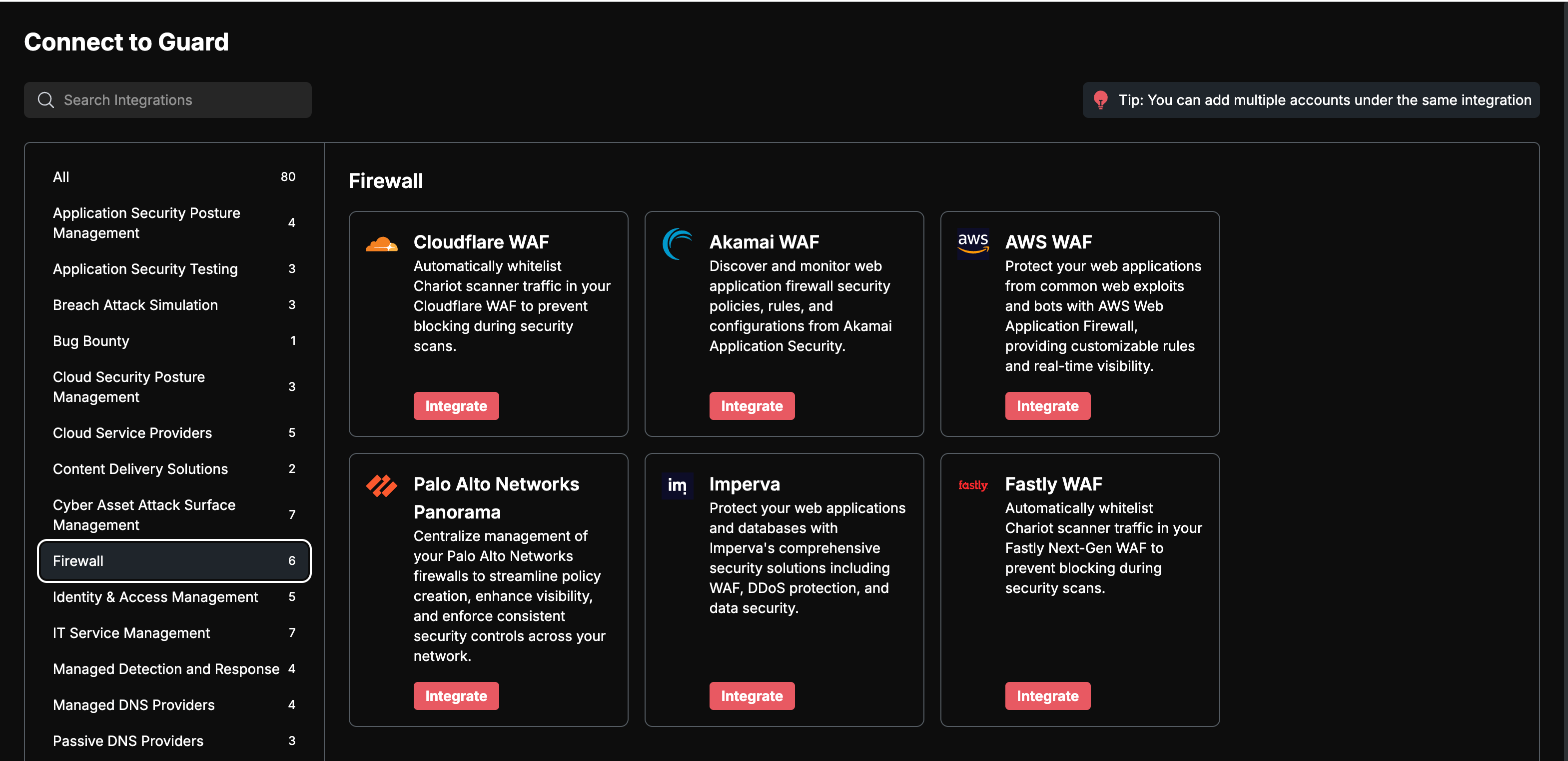
Click Integrate on Palo Alto Network Panorama Card
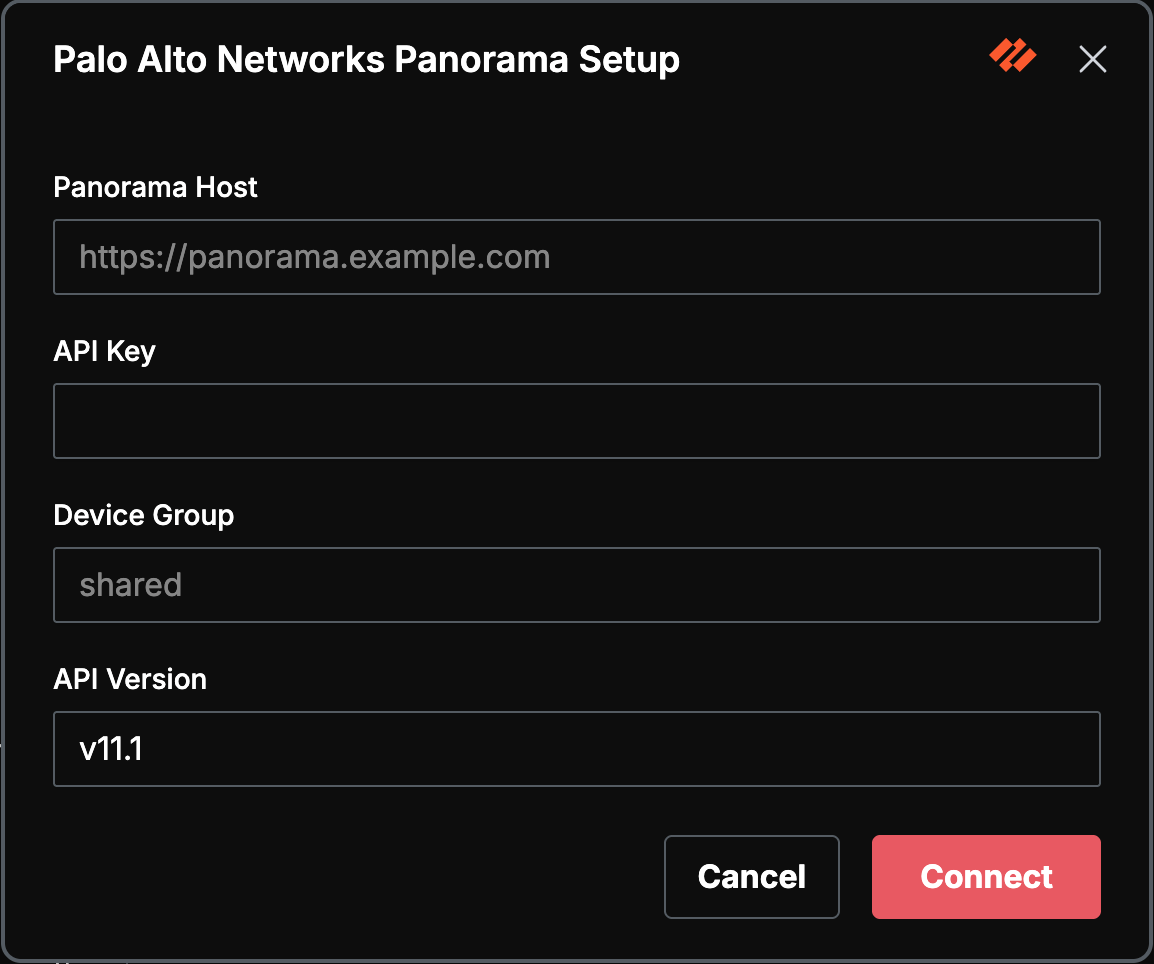
Enter values for the following fields and click connect.
Click Connect. PGP validates your credentials by making a lightweight test call to the Panorama API (
Objects/Addresses?limit=1). If validation succeeds, the integration begins importing address objects on its next scheduled run.
What Data Is Synced
Address Objects to PGP Assets
Every address object in your configured scope (device group or shared) is imported as a PGP asset
Assets are tagged with the
paloaltocloud service identifierEach asset retains a reference to its Panorama device group and object name for traceability
On subsequent runs, PGP reconciles the current Panorama state — new objects are added, removed objects are detected via affiliation checks
Address Groups (Metadata Only)
Static and dynamic address groups are enumerated for context
Group membership data enriches the understanding of how your firewall policies organize assets
Groups themselves are not created as standalone assets
Panorama API Endpoints Used
Both endpoints accept location=shared or location=device-group&device-group={name} to control scope.
Troubleshooting
Security and Data Handling
PGP uses your API key exclusively for read-only REST API calls — it never modifies any configuration, policies, address objects, or other settings in Panorama
The API key is encrypted at rest and in transit within your PGP deployment
Only address object metadata is imported (names, IPs, FQDNs, tags, descriptions) — no firewall logs, traffic data, or credentials are accessed
PGP authenticates via the
X-PAN-KEYHTTP header over HTTPS; the API key is never logged or exposed in error messages
Coming Soon
We are actively expanding the Panorama integration to provide deeper visibility into your firewall-managed environment:
NAT Rule Extraction — Discover externally-exposed services by analyzing destination NAT rules. DNAT rules that route internet traffic to internal servers reveal assets that may not appear as standalone address objects.
Security Policy Analysis — Extract firewall security rules to understand which assets are intentionally exposed and what applications and services are allowed through your perimeter.
Firewall Rule Auditing — Identify common misconfigurations such as overly permissive rules (any-any), allow rules missing security profiles (antivirus, anti-spyware, vulnerability protection), and unused or shadowed rules. These findings will surface as risks in PGP alongside your vulnerability data.
Network Topology Discovery — Import interface configurations, zone definitions, and GlobalProtect VPN gateway addresses to build a more complete picture of your network perimeter and its security boundaries.
Integration category: Firewall. Data direction: Read-only (Panorama to PGP). Authentication: API key via X-PAN-KEY header.