Microsoft Azure - IaC Deployment (Recommended)
Microsoft Azure - IaC Deployment (Recommended)
This guide walks you through connecting your Azure environment to the Praetorian Guard Platform (PGP) for comprehensive security monitoring and management using Infrastructure as Code (IaC) deployment methods. The integration uses Azure's federated identity credentials and role-based access control to provide PGP with the necessary permissions to assess your Azure resources while maintaining security best practices.
You can choose between tenant-level integration (recommended for full Azure environment coverage) or subscription-level integration (for specific subscription monitoring). The process involves creating an Azure AD app registration, configuring the appropriate permissions, and validating the connection through automated Terraform deployment.
Prerequisites
Before starting the integration, ensure you have:
Azure portal access as a Global Administrator permissions to create app registrations and assign roles
Global Administrator permissions are necessary for creating app registrations and granting admin consent
User Access Administrator permissions are required for tenant-level integration role assignments at tenant root
Subscription Owner or User Access Administrator permissions for subscription-level integration
Terraform is required
Integration Process
Step 1: Initiate Integration Setup
Navigate to the Integrations section in your PGP dashboard
Click "Add Integration" and select "Azure"
Choose your integration scope and provide the required information
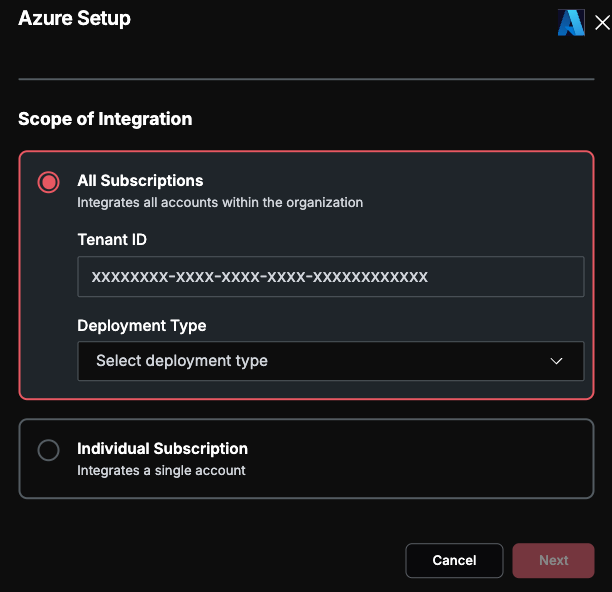
Tenant-Level Integration (Recommended)
For tenant-level integration, you'll need to provide:
Tenant ID: Your Azure AD tenant ID (GUID format)
Deployment Type: Choose Terraform
TIP: To get your Tenant ID, navigate to Azure Active Directory (or Microsoft Entra ID) in the Azure Portal. The tenant ID is displayed in the Overview section, or you can find it in the URL when viewing your directory.
Subscription-Level Integration
For subscription-level integration, you'll need to provide:
Tenant ID: Your Azure AD tenant ID (GUID format)
Subscription ID: The specific Azure subscription ID you want to integrate
Deployment Type: Choose Terraform
Step 2: Download Integration Template
After providing your tenant information, PGP will generate the appropriate deployment template. This template is generated dynamically based on the information you provided.
Click "Download IAC Template" to download the deployment files
The template contains the app registration configuration, federated credentials, and role assignments pre-configured with your unique subject ID
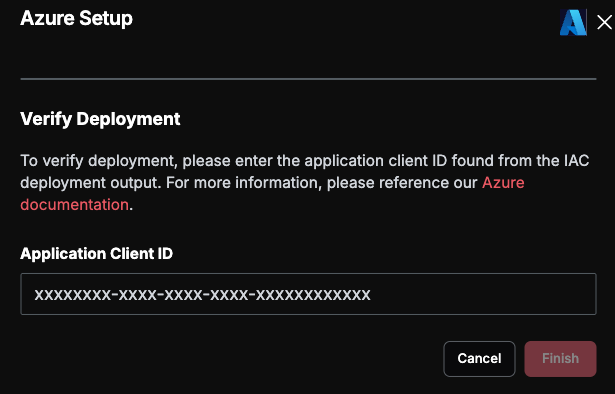
On submission, the next step will ask for an "Application ID", which you will get after completing the infrastructure deployment
Step 3: Deploy the Template
Perform the necessary tasks based on the deployment task you chose above. Please make sure to complete this deployment successfully before completing the integration.
Terraform Deployment (Recommended)
Open Azure Cloud Shell or ensure you're authenticated to Azure within your workstation (you will need to ensure Terraform is installed; Azure Cloud Shell comes pre-installed with Terraform).
Ensure that the credentials you signed in with possess the necessary administrator privileges:
Global Administrator
User Access Administrator
Subscription Owner (for subscription-level integration)
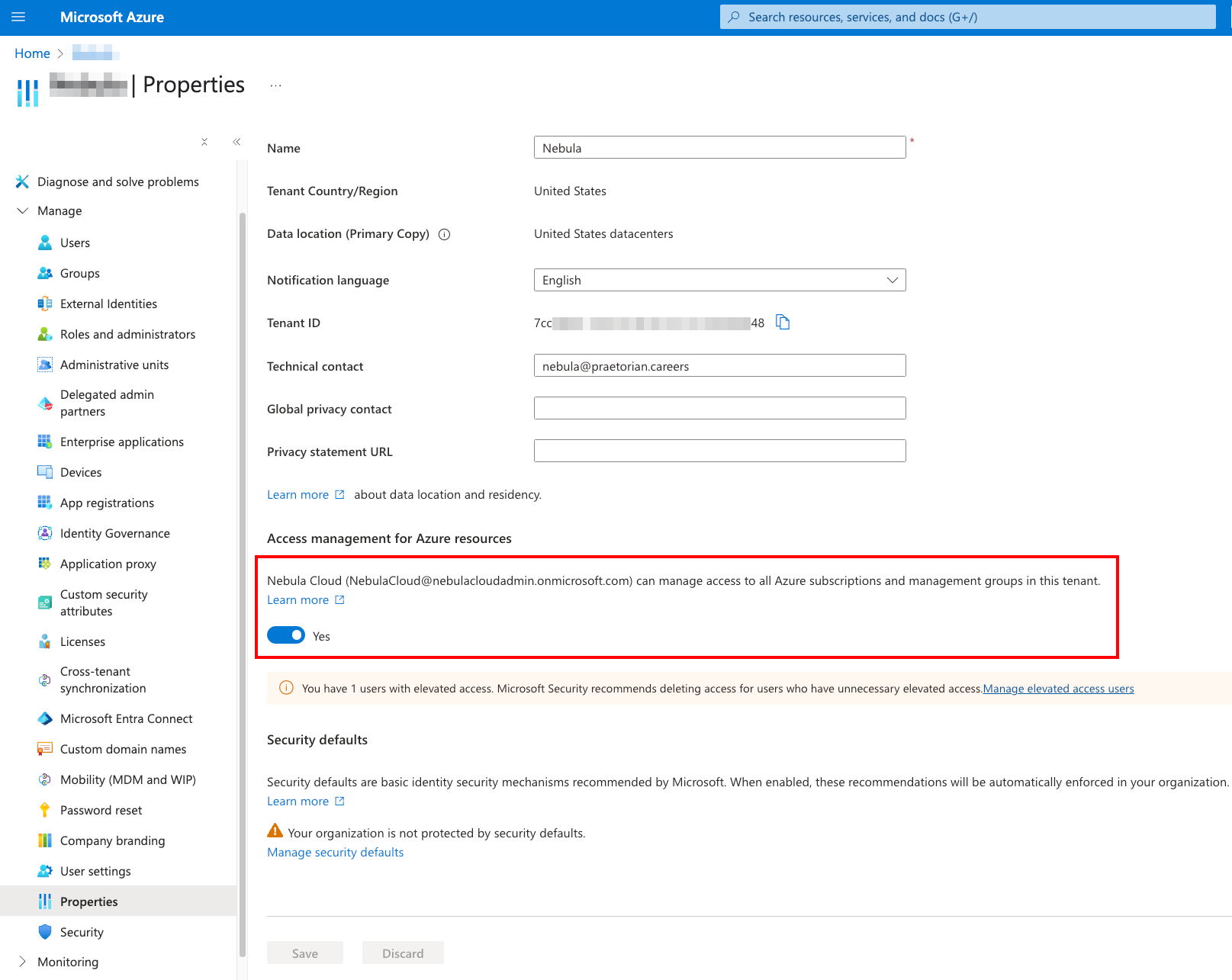
If you're integrating at the tenant level, ensure you have access to manage the tenant root management group. To be able to consent to the new application at the tenant root level, you need to grant yourself User Access Administrator, even as a Global Administrator. See the following screenshot to identify where to enable that access:
If you're integrating a single subscription, set CLI to use that subscription:
az account set --subscription "YOUR_SUBSCRIPTION_ID"Create a new directory, initialize Terraform, and create a plan:
mkdir PGP-deployment && cd PGP-deploymentUpload the template from previous step to this directory
terraform init && terraform planReview the planned changes and save to a file if necessary. Once satisfied, apply the changes and monitor for deployment errors:
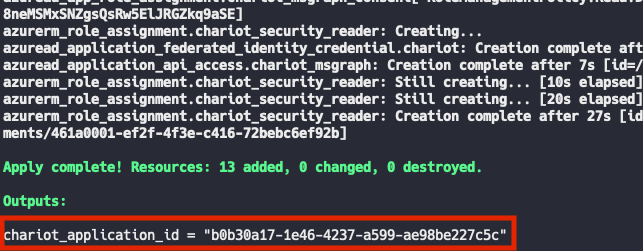
terraform applyEnsure there are no errors during deployment, then observe the output at the end of the execution output. The deployment will produce an Application ID, which you need to provide back to PGP.
Under the hood, the Terraform template performs a number of actions. More specifically, for the tenant-level integration, the template will:
Create an Azure AD app registration for PGP and its service principal
Automatically grant admin consent for all API permissions
Set up federated identity credential with PGP's Cognito pool and your unique subject identifier
Configure required Microsoft Graph API permissions
Assign Security Reader role at tenant root management group scope
Elevate access to manage all Azure subscriptions and management groups
For a subscription-level integration, the template will perform similar actions:
Similar steps as the tenant-level permissions
Assign Security Reader role at the specific subscription scope selected for integration
Step 4: Complete Integration
After deploying the template or completing manual setup, return to the PGP integration modal
Enter the Application ID value provided as an output of your deployment
Click "Finish" to complete the integration
PGP will automatically:
Validate the integration by authenticating with Cognito
Perform OIDC token exchange with Azure Entra ID for both ARM and Microsoft Graph tokens
Verify validity of access using simple Azure API calls
Add the integration to your integrations list upon successful validation
Extending Your Azure Integration with Azure DevOps
Once you have completed the Azure cloud integration above, you can extend it to include Azure DevOps for repository scanning and work item management. This approach uses Azure Entra ID authentication through the same Guard Application created by the Terraform template, which is more secure than standalone PAT-based authentication.
Adding the Guard Application to Azure DevOps
To enable Azure DevOps integration through your existing Azure cloud connection, you will need to manually add the Guard Application ID (output from the Terraform deployment) to Azure DevOps and configure the appropriate access.
Set Access Level: Add the Guard Application as a user in your Azure DevOps organization and assign it access level “Basic”.
Grant Access to Projects: Provide the Guard Application with access to the desired Azure DevOps projects that you want PGP to scan.
Configure Group Permissions: Add the Guard Application to the correct security group within those projects. At a minimum, the application needs Read access for repository discovery and secret scanning. If you also want PGP to create and manage Azure DevOps Work Items for security findings, Read & Write access is required.
Permissions Are Environment-Specific — The exact steps to configure these permissions depend heavily on your organization's Azure DevOps permissions setup. You may need to create a separate security group or a dedicated Area within the Board for Guard to be able to create and read issues. Consult your Azure DevOps administrator if you are unsure about the correct group or area configuration.
What This Enables
Repository Discovery & Secret Scanning (Read access): PGP will discover your Azure DevOps Git repositories and scan them for hardcoded secrets and credentials using Titus.
Work Item Ticketing (Read & Write access): PGP can automatically create Azure DevOps Work Items for discovered security findings and sync their status bidirectionally.
Support and Troubleshooting
If you encounter any issues during the Azure integration process or need additional assistance, our support team is here to help. Please don't hesitate to reach out to support@praetorian.com with:
Details about your integration setup (tenant-level or subscription-level)
Any error messages encountered during deployment
Screenshots of relevant Azure portal configurations
Your Application ID and Tenant ID for reference
Our team will work with you to resolve any integration challenges and ensure your Azure environment is properly connected to PGP for comprehensive security monitoring.
Extending Your Azure Integration with Azure DevOps
Once you have completed the Azure cloud integration above, you can extend it to include Azure DevOps for repository scanning and work item management. This approach uses Azure Entra ID authentication through the same Guard Application created by the Terraform template, which is more secure than standalone PAT-based authentication.
Adding the Guard Application to Azure DevOps
To enable Azure DevOps integration through your existing Azure cloud connection, you will need to manually add the Guard Application ID (output from the Terraform deployment) to Azure DevOps and configure the appropriate access.
Set Access Level: Add the Guard Application as a user in your Azure DevOps organization and assign it an appropriate access level (e.g., Basic or Stakeholder, depending on required capabilities).
Grant Access to Projects: Provide the Guard Application with access to the desired Azure DevOps projects that you want PGP to scan.
Configure Group Permissions: Add the Guard Application to the correct security group within those projects. At a minimum, the application needs Read access for repository discovery and secret scanning. If you also want PGP to create and manage Azure DevOps Work Items for security findings, Read & Write access is required.
Permissions Are Environment-Specific — The exact steps to configure these permissions depend heavily on your organization's Azure DevOps permissions setup. You may need to create a separate security group or a dedicated Area within the Board for Guard to be able to create and read issues. Consult your Azure DevOps administrator if you are unsure about the correct group or area configuration.
What This Enables
Repository Discovery & Secret Scanning (Read access): PGP will discover your Azure DevOps Git repositories and scan them for hardcoded secrets and credentials using Titus.
Work Item Ticketing (Read & Write access): PGP can automatically create Azure DevOps Work Items for discovered security findings and sync their status bidirectionally.