Integrations Overview
Integrating Your Tech Stack With Praetorian Guard
Organizations face increasingly complex security challenges across diverse technology environments. Third-party integrations serve as vital connectors that enhance security operations by consolidating critical data and automating key workflows across platforms. By leveraging integrations, security teams can:
Achieve Comprehensive Visibility: Combine data from multiple security tools and platforms to build a complete picture of your security posture
Accelerate Response Times: Automate the sharing of threat intelligence and security alerts across systems to enable faster incident detection and response
Reduce Manual Effort: Eliminate the need to manually collect and correlate data across different security tools
Enhance Decision Making: Access enriched context and detailed insights by combining data from multiple specialized security platforms
Scale Security Operations: Handle growing security demands without proportionally increasing staff by automating routine tasks
Standardize Processes: Ensure consistent security practices by integrating tools into standardized workflows
Through strategic integration of third-party platforms, organizations can build a more robust and efficient security program that maximizes the value of their security investments while improving their overall security posture.
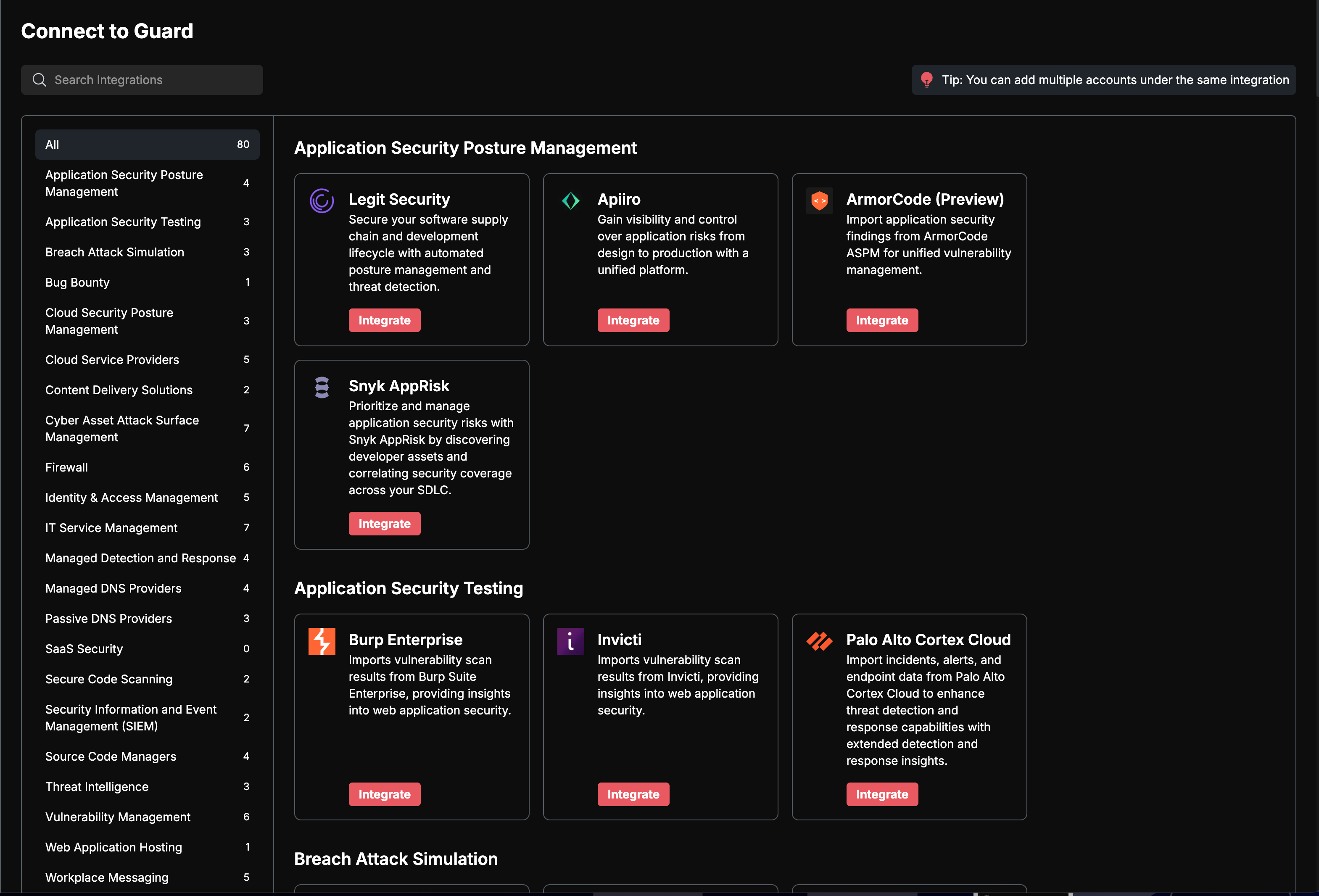
The Integrations Page
When you first access the integrations page, the Add Integrations will present a collection of integration cards organized by their primary functions. These integrations span across attack surface discovery, risk notifications, vulnerability scanning, and more. Each integration card displays the service's logo and name, making it easy to locate your desired integration.
Understanding Integration Types
The platform supports several core types of integrations that serve different purposes in your security workflow. Attack surface integrations help you discover and monitor your infrastructure, including cloud services like AWS, Azure, and GCP, as well as code repositories through GitHub and GitLab. These integrations provide continuous visibility into your expanding digital footprint.
For structured workflow management, ticketing system integrations with platforms like Jira and ServiceNow help track and resolve identified risks systematically.
Vulnerability scanning integrations enhance your security assessment capabilities. The platform supports major scanning tools including Nessus, Burp Enterprise, and Qualys. You can either connect these scanners directly or import scan results through dedicated import interfaces.
Configuring Integrations
The configuration process follows a consistent pattern across all integrations while accommodating their unique requirements. To begin setting up an integration, click on its card to open the configuration interface. The interface will present you with specific fields needed for that service.
For detailed instructions on how to set up each integration, look for documentation in the Integrations section of the documentation.
For cloud provider integrations, the setup typically involves authentication and access configuration. AWS integration uses a CloudFormation stack deployment process – you'll find a "Launch CloudFormation Stack" button that streamlines the setup. For Azure, you'll need to provide your Application ID, Secret Value, and Tenant ID. GCP configuration requires a Project ID and Service Account JSON keyfile.
Source code management integrations offer flexible setup options. With GitHub, you can choose between installing the GitHub App directly or providing a Personal Access Token (PAT) along with your organization URL. GitLab setup focuses on PAT authentication and requires your GitLab Group URL.
Notification service configurations emphasize ease of use while ensuring secure communication. Slack integration requires a webhook URL and severity level selection. The severity options range from Info to Critical, allowing you to filter notifications based on risk importance. Similar configuration patterns apply to other messaging platforms like Microsoft Teams and Google Chat.
Security Considerations
When configuring integrations, the platform encourages secure authentication practices. Wherever possible, use API tokens or service accounts with appropriately scoped permissions. For services that require direct credential input, the platform securely handles sensitive information through encrypted fields.
Most integrations include severity level configuration, which helps manage notification volume and focus attention on significant risks. Consider your organization's needs when selecting these thresholds – setting them too low might lead to alert fatigue, while setting them too high could cause you to miss important notifications.
The Praetorian Guard Platform (PGP) offers integrations with service providers in the following categories:
Breach Attack Simulation
Tools that simulate cyber attacks to test security defenses and identify vulnerabilities in systems and networks.
Cloud Security Posture Management
Solutions that continuously monitor cloud infrastructure to identify and remediate security risks, compliance issues, and misconfigurations.
Cyber Asset Attack Surface Management
Platforms that help organizations discover, monitor, and manage their external attack surface and digital asset inventory.
Cloud Service Providers
Major cloud computing platforms that provide infrastructure, platform, and software services.
Content Delivery Solutions
Services that distribute content to users through a network of geographically distributed servers to improve performance and reliability.
Firewall
Network security systems that monitor and control incoming and outgoing network traffic based on predetermined security rules.
IT Service Management
Tools for managing IT services, incidents, problems, changes, and service requests across an organization.
Managed Detection and Response (MDR)
Services that provide 24/7 threat monitoring, detection, and response capabilities managed by security experts.
Managed DNS Providers
Services that manage Domain Name System (DNS) infrastructure to ensure reliable and secure domain name resolution.
Passive DNS Providers
Services that collect and analyze historical DNS resolution data to support security investigations and threat detection.
Knowledge Bases
Platforms that store and organize organizational knowledge, documentation, and collaborative content. PGP scans these platforms for exposed secrets and sensitive information.
Source Code Managers
Platforms that track and manage changes to source code repositories while facilitating collaboration among developers.
Vulnerability Management
Solutions that identify, evaluate, report on, and remediate security vulnerabilities across systems and applications.
Getting Help
Throughout the integration interface, you'll find contextual help through "Learn more" links. These resources provide detailed, service-specific setup instructions and troubleshooting guidance. When configuring complex integrations like cloud providers or enterprise security tools, these resources can help ensure proper setup and optimal use of the integration features.
For technical issues during setup, verify that all required fields are properly filled and that provided credentials have necessary permissions. Many integration issues stem from incorrect URLs or network access restrictions, so consider these factors when troubleshooting connection problems.
Support
If you encounter any difficulties or have questions about setting up integrations, our support team is here to help. Our team is committed to helping you maximize the value of your integrations. For help, please reach out to support@praetorian.com.